First it was the NSA’s turn, and now the CIA gets its Wikileaks moment. Claiming it to be the “largest intelligence publication in history,” Wikileaks has released its first installment of documents that expose the CIA’s cyberespionage efforts. If genuine, the documents unveil operations, locations, and methods that could cripple US efforts on cyberwarfare:
The first full part of the series, “Year Zero”, comprises 8,761 documents and files from an isolated, high-security network situated inside the CIA’s Center for Cyber Intelligence in Langley, Virgina. It follows an introductory disclosure last month of CIA targeting French political parties and candidates in the lead up to the 2012 presidential election.
Recently, the CIA lost control of the majority of its hacking arsenal including malware, viruses, trojans, weaponized “zero day” exploits, malware remote control systems and associated documentation. This extraordinary collection, which amounts to more than several hundred million lines of code, gives its possessor the entire hacking capacity of the CIA. The archive appears to have been circulated among former U.S. government hackers and contractors in an unauthorized manner, one of whom has provided WikiLeaks with portions of the archive.
“Year Zero” introduces the scope and direction of the CIA’s global covert hacking program, its malware arsenal and dozens of “zero day” weaponized exploits against a wide range of U.S. and European company products, include Apple’s iPhone, Google’s Android and Microsoft’s Windows and even Samsung TVs, which are turned into covert microphones.
The biggest takeaway may not be the programs involved, about which more in a moment, but the claim that the CIA has lost control of “a majority of its hacking arsenal.” Ironically or not, losing control of these documents tends to support that claim and suggest that the problem is systemic — if indeed these documents are what Wikileaks purports them to be. The first question for claims of leaks is always whether the information is genuine. Politico notes that the embarrassment potential is rather high if these documents turn out to be authentic. Don’t ask the CIA that question, though, because they’re not going to answer it — ever:
If the files are genuine, their release marks the latest embarrassing episode for the intelligence community. Last year, a group calling itself “the Shadow Brokers” released classified NSA hacking tools that revealed so-called “zero-day” exploits, or unknown code flaws in popular products the government is exploiting.
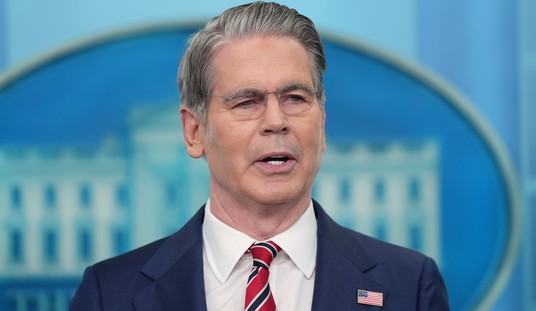
CIA spokesman Jonathan Liu told POLITICO, “We do not comment on the authenticity or content of purported intelligence documents.”
The intelligence communities in the US already find themselves in the spotlight over leaks, although not in the context of its operations as much as potential political interference. This, assuming it’s legit, marks another kind of issue that has become a theme over the past few years — the security measures to protect highly classified information. A quick read of the Wikileaks descriptions of the documents make it very clear that these operations would have had a high degree of security attached to them.
That poses another obvious question: Where did Wikileaks get this tranche of documents? This haul involved a number of programs and tools, so the source had to be someone highly placed in the hierarchy, or perhaps a lower-level employee with far too much access. The latter scenario suggests another Edward Snowden, if it indeed is a single source as Wikileaks claims:
In a statement to WikiLeaks the source details policy questions that they say urgently need to be debated in public, including whether the CIA’s hacking capabilities exceed its mandated powers and the problem of public oversight of the agency. The source wishes to initiate a public debate about the security, creation, use, proliferation and democratic control of cyberweapons.
Those may be important issues, but so is operational security at the NSA and CIA. Wikileaks reports that these documents came to them in 2016, and that more are on their way, potentially from other sources. That would have been three years after Snowden absconded with a massive amount of data from the NSA, an event which should have prompted the CIA and other intel agencies to tighten their security. Clearly more work needs to be done along those lines.
The data itself is a James Bondian smorgasbord of technical feats — hacking Samsung smart TVs to turn them into bugging devices (“Weeping Angel”), gaining real-time access to smart cars, and disguising their operations as hacks from other sources (“UMBRAGE”). Wikileaks alleges that the CIA and NSA have conducted a turf war for supremacy in cyberwarfare, and argues that the CIA is now winning that internecine fight based on the evidence they’ve released. That could be a result of Wikileaks’ own exposure of NSA materials four years ago, which raises more questions about whether this release might be part of the infighting between the two agencies, too.
There are lots and lots of rabbit holes here in which we could get lost for a long time. If Wikileaks is correct that the CIA has lost control of its Bondian smorgasbord, a lot more of us will get lost in them than we know.






Join the conversation as a VIP Member