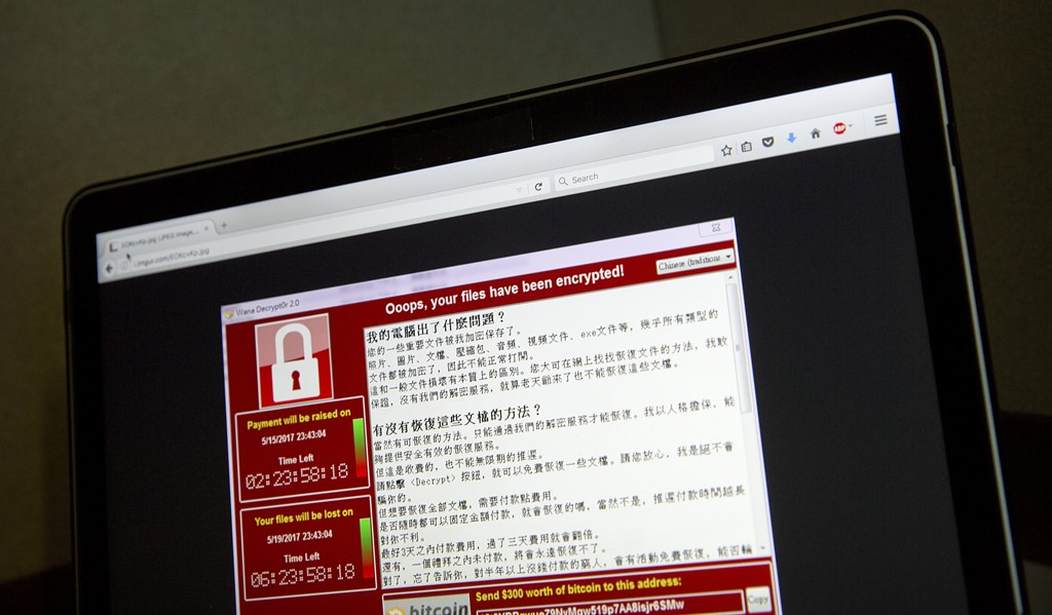
A researcher at Google announced Monday that he had identified some common code in the Wanna Cry ransomware and hacking tools used by the Lazarus Group. The Lazarus Group is believed to be connected to North Korea and was involved in the 2014 hack of Sony Pictures. Here’s the cryptic tweet highlighting the similarities:
9c7c7149387a1c79679a87dd1ba755bc @ 0x402560, 0x40F598
ac21c8ad899727137c4b94458d7aa8d8 @ 0x10004ba0, 0x10012AA4#WannaCryptAttribution— Neel Mehta (@neelmehta) May 15, 2017
From Ars Technica:
The tweet referenced identical code found in a WCry sample from February and an early 2015 version of Cantopee, a malicious backdoor used by Lazarus Group, a hacking team that has been operating since at least 2011…
WCry’s creators may have deliberately added code found in Cantopee in an attempt to trick researchers into mistakenly believing Lazarus Group is behind the ransomware. Researchers at antivirus provider Kaspersky Lab said such a “false flag” is plausible but improbable. The Cantopee code snippet, the researchers explained, was removed from later versions of WCry, making it hard to spot and hence ill-suited to act as a decoy…
“This opens a lot of possibilities for everyone to find other similarities between all versions of WannaCrypt that have been found so far, and the tools used by Lazarus,” Maarten van Dantzig, a researcher at FOX-IT, told Ars.
Another clue that Wanna Cry was the work of a government: It contained a killswitch in the form of a hidden Url that, once registered, stopped the ransomware from spreading. Jazz wrote about the cyber researcher at Kryptos Logic who discovered the Url yesterday. Ars Technica notes, “Such ‘killswitches’ are highly unusual for malware developed by financially motivated criminal groups. By contrast, they’re much more common in malware written by nation-sponsored hackers.”
In addition to the Sony Pictures hack, the Lazarus Group has been implicated in the theft of $81 million dollars from Bangladesh’s account at the Federal Reserve Bank of New York last year. The theft actually attempted to take nearly a billion dollars but most of the transactions were canceled after an alert banker noticed a typo.






Join the conversation as a VIP Member